Today I want to show you how to encrypt a Windows drive. Why should you encrypt a drive? Basically to prevent your data from being read by unauthorized persons, that may happen for example if your laptop or external USB drive is stolen.
So if you want to encrypt your drive, Bitlocker is your friend.
But what is Bitlocker?
Bitlocker is a Windows feature available in various Windows versions, among them Windows 10 Pro, and unfortunately not available in Windows 10 Home. You can use it to encrypt your Windows boot drive or an external USB drive.
In our example we will use it to configure an external USB drive.
We will check togheter each single configuration step.
Once you have connected your USB drive, click on the “This PC” icon on desktop, and then right click on the drive you want to encrypt. We want to encrypt the drive “Maxtor (D:)”. So right click the corresponding icon and in the context menu click on “Turn on BitLocker”.

A wizard will start asking you to choose the password that will be used to encrypt the drive:
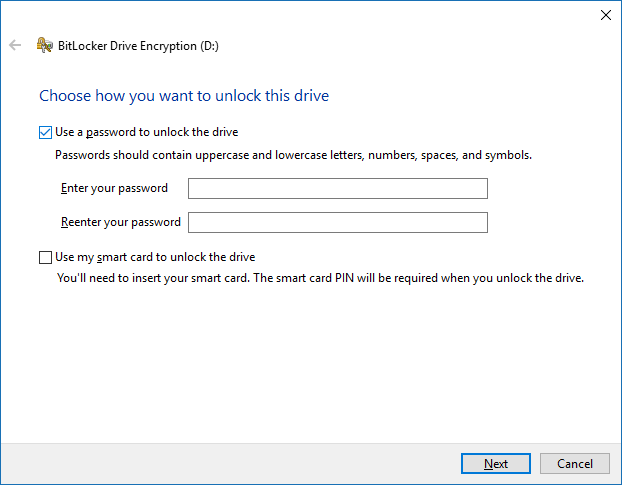
Once the password has been chosen, you can click “Next”. In the next step of the wizard you have to select how to store your recovery key. As explained in the window, the recovery key allows you to decrypt your file even if forget your password.
I usually select the option “Save to a file” and keep the file in a safe place.

In the next step you have to select how much of your drive you want to encrypt, as you can see in the following screenshot:

In my opinion the option “Encrypt used disk space only (faster and best for new PCs and drives)” is fine in most cases. But keep in mind that this option make possible to recover the files deleted before the encryption of the drive.
Now you have to choose which encryption mode you want to use:

Since we are encrypting a removable drive I choose the option “Compatible mode (best for drives that can be moved from this device)” to maximize compatibility when I move the drive to another PC. I suggest to use the first option if you encrypt a fixed drive.
In the next step you only have to click “Start encrypting” to begin the encryption of the drive.
…. and then wait some time….

Consider that, depending on how full the disk is, you may have to wait a few hours…
Completed the encryption, if you look at your drive list, you will se a padlock near your encrypted drive.

If you double click the drive, you will be asked to insert the password to unlock the drive:
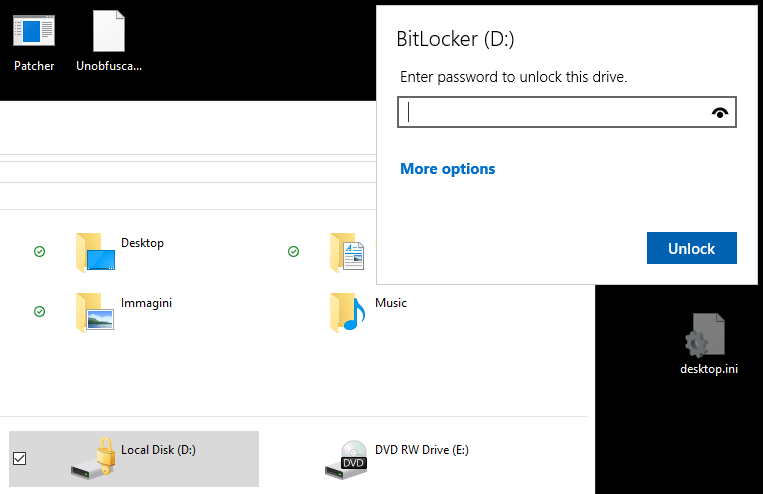
Insert your password to unlock the drive.
After that you will be able to access your data.